AI-assisted engineering
Governed Agentic Architecture: Spec-Driven Automation for Scalable Infrastructure Systems
Explains how to make agentic systems useful for infrastructure and engineering workflows by pairing intention, tools, permissions, tests, and acceptance evidence.

Decision brief
Use this article as a routing artifact, not passive content.
Read time
4 min
Updated
May 30, 2026
Route
AI-assisted engineering
Why it matters
Explains how to make agentic systems useful for infrastructure and engineering workflows by pairing intention, tools, permissions, tests, and acceptance evidence. The useful signal is the operating judgment behind the topic: scope, data boundaries, proof, UAT, and handoff.
Best lens
Read it through Autodesk API, CAD Automation, AI Systems and decide which service, proof artifact, or leadership conversation it supports.
Next action
Connect the writing to resume evidence, flagship outcomes, and staff-level engineering software fit.
Review software leadership proofContentsJump sections
Evaluation note
Explains how to make agentic systems useful for infrastructure and engineering workflows by pairing intention, tools, permissions, tests, and acceptance evidence. Use it as a practical routing note: what problem is being described, what infrastructure is required, what guardrails matter, and what proof a buyer or hiring manager should ask to see.
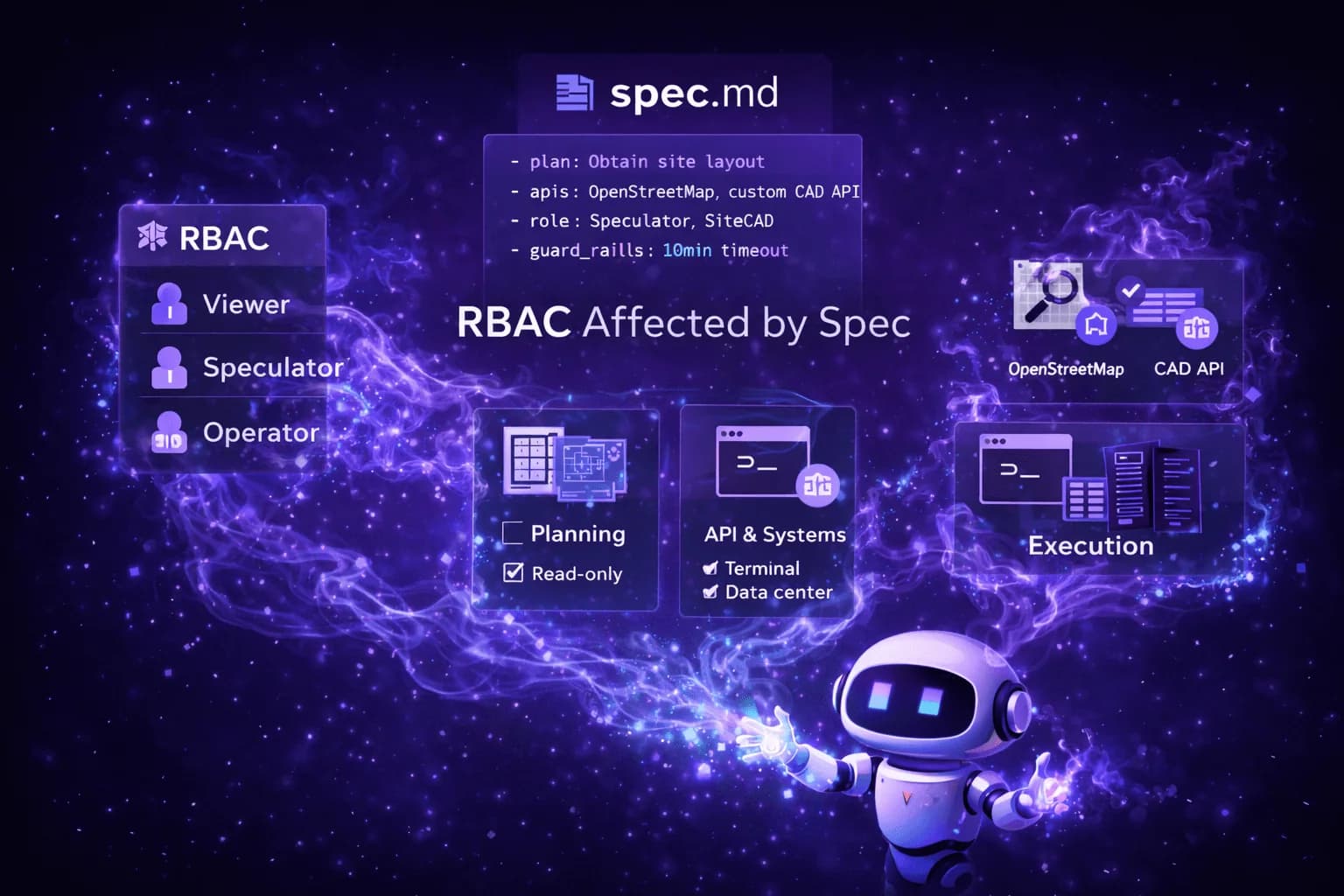
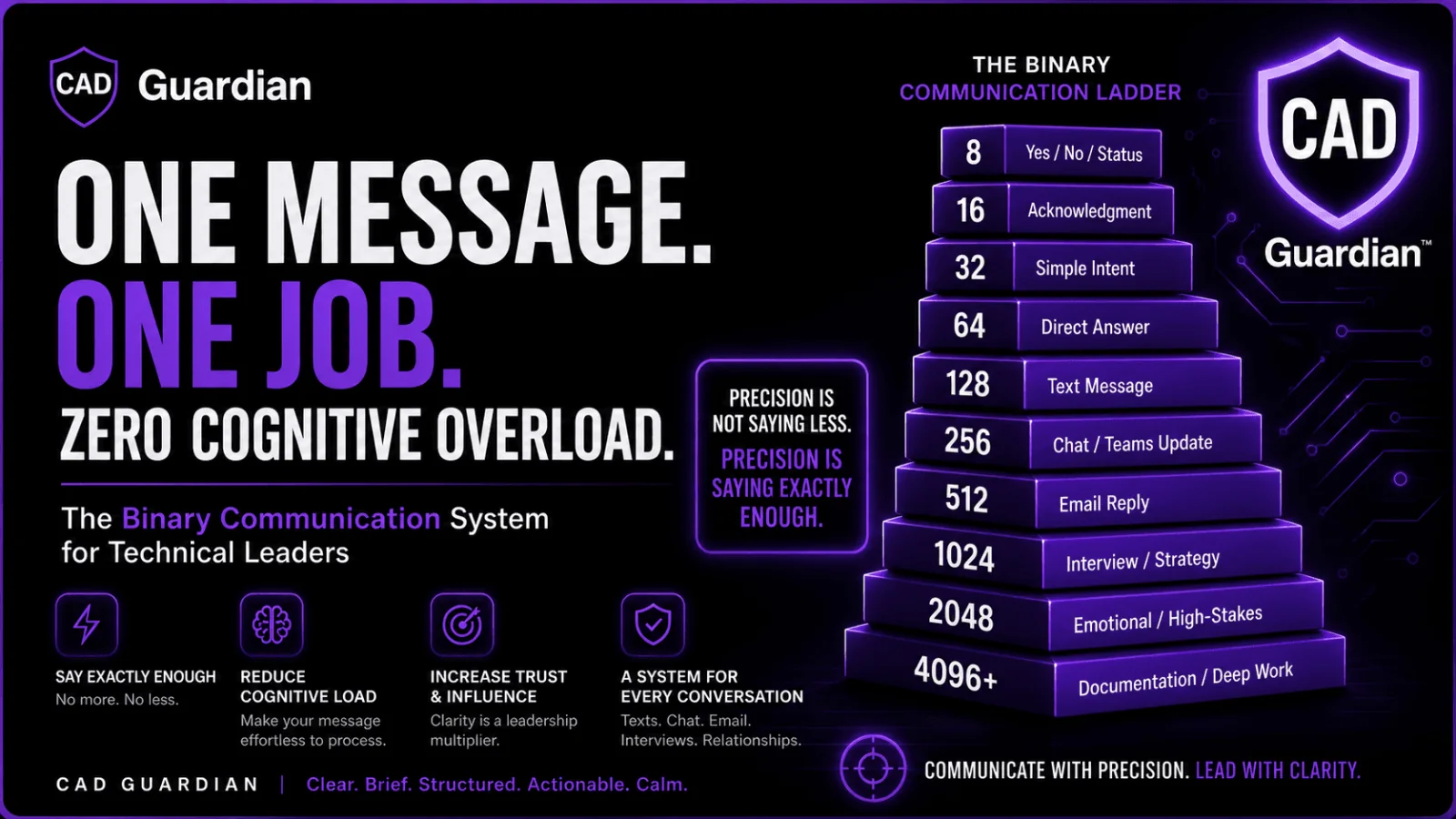
CAD Guardian field context
This article is about putting rails around agentic work. The useful version of AI automation is not an unsupervised bot; it is a tool-using system with a spec, permissions, review gates, and proof that a human can accept.
- Usefulness: turns scattered expertise into reusable decisions, plans, checklists, code reviews, media, and evidence without removing human accountability.
- Infrastructure: clear prompts, source boundaries, approved tools, private-data rules, model selection, review loops, and artifact-based validation.
- Guardrails: least-privilege access, private-data minimization, approved AI-use boundaries, test data, UAT, runtime proof, and written acceptance criteria.
- Who benefits: lean engineering teams, CAD automation developers, technical peers, operators, and buyers trying to understand what AI systems are doing.
Most teams experimenting with AI agents are automating instability.
In data center environments, that approach fails immediately.
Last week I implemented a spec-driven agent architecture designed for governed execution across a cross-platform monorepo (mobile, web, API). The objective was not novelty. It was deterministic, production-safe automation.
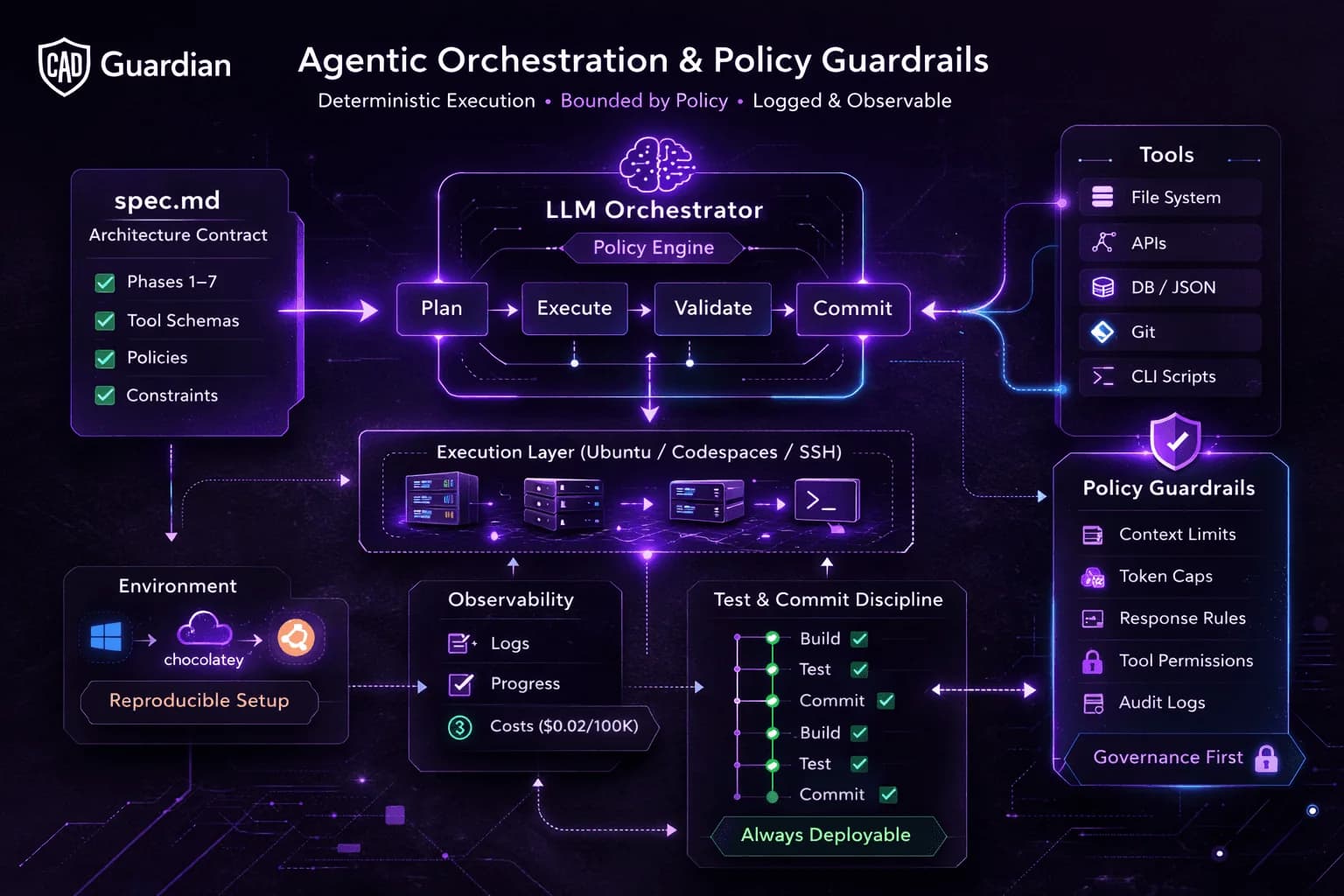
Architecture Principles
- Spec (spec.md) generated first, implementation executed against it
- Policy-governed LLM execution (context caps, token ceilings, response limits)
- Deterministic sequential execution with structured progress logs
- Environment auto-provisioning with launch configuration control
- Small logical git commits — buildable and test-passing at every checkpoint
API cost held to ~$0.02 per 100K tokens through strict policy enforcement.
This was not prompt engineering.
It was system orchestration.
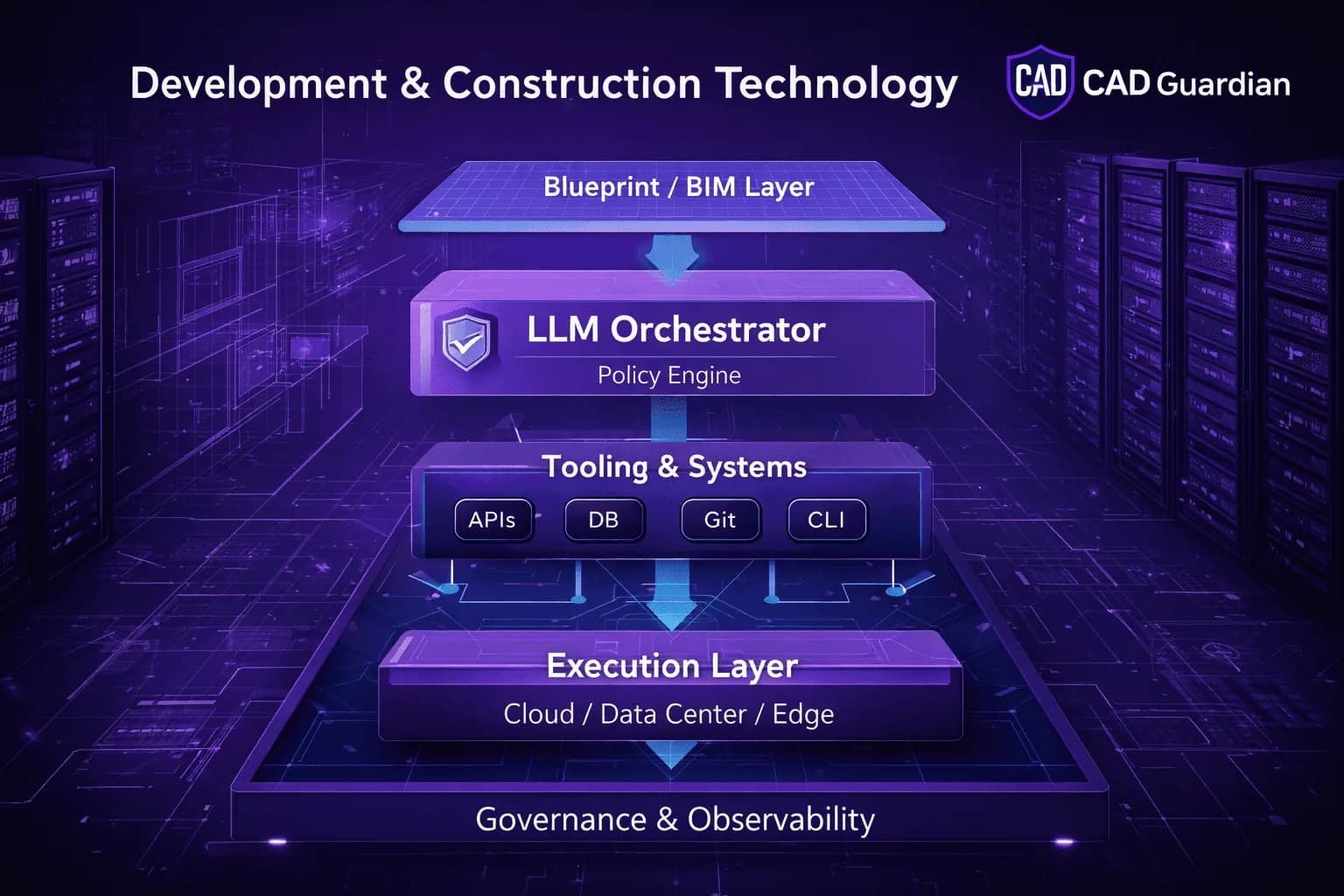
Why This Matters for Development & Construction Technology
In large-scale infrastructure environments:
- Tooling must be interoperable
- Changes must be reversible
- Automation must be observable
- Systems must remain deployable at every state
- Governance must precede scale
The agent architecture I built reflects those principles:
Agent
├── Tools
├── File System
├── Messaging Layer
├── Execution Layer
└── Policy & Guardrails
Every action is logged.
Every change is testable.
Every execution path is bounded by policy.
That is how automation becomes enterprise-safe.
Hard Lesson Reinforced
CSS drift, unchecked commits, and uncontrolled execution are small examples of the same macro problem:
Entropy without governance.
The solution is architectural discipline.
Spec > vibe.
Determinism > improvisation.
Governed automation > reactive maintenance.
I’ll be publishing a minimal public MVP (<3K LOC) to demonstrate the pattern in a consumable format.
For teams building scalable data and lifecycle systems — this is the direction.
Bonus Nerd Section
(Non-technical readers: skip this. Implementation layer below.)
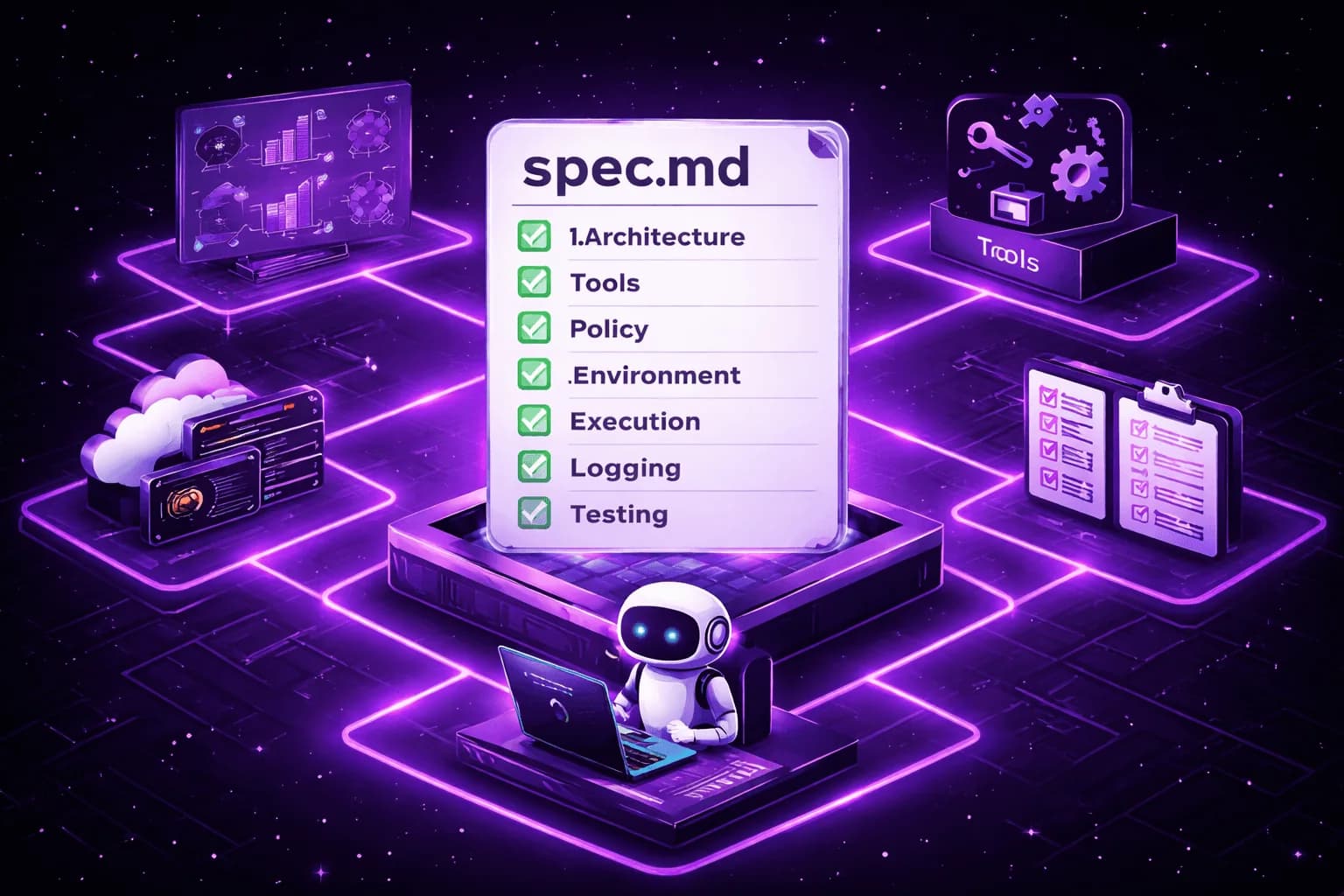
This project wasn’t just coding. It was controlled implementation leadership.
I led the build across 7 spec phases with Codex CLI 5.3, treating the repo like infrastructure:
- Architecture definition
- Tool contracts + schema enforcement
- Policy governance (context, tokens, response caps)
- Environment provisioning
- Execution orchestration
- Observability + logging
- Test + commit discipline
Each phase had a written spec. The agent executed against the spec. No improvisation.
Environment as Code (Chocolatey + Ubuntu)
On Windows, I used Chocolatey to bootstrap the full environment:
choco install nodejs pnpm git python vscodeWhy this matters:
- Deterministic machine setup
- Reproducible onboarding
- Minimal manual configuration
- Faster parity across contributors
Enterprise takeaway:
If you cannot rebuild your environment from scratch in minutes, you don’t own it.
From there:
- SSH into Ubuntu VM from VS Code
- Or spin up GitHub Codespaces
- Run the monorepo remotely
- Access the running app from a phone browser over LAN
Device becomes client.
Environment remains controlled.
Spec-Driven Execution (Codex CLI)
The flow:
- Generate spec.md
- Execute sequentially
- Print structured progress checklist
- Auto-install dependencies
- Write launch.json
- Keep the repo buildable
- Commit in small logical increments
Every commit:
- Builds
- Passes tests
- Preserves deployability
That’s not vibe coding.
That’s change management.
TailwindCSS Governance
No inline CSS. Period.
Why:
- Inline styles bypass design contracts
- Cascade order becomes unpredictable
- Redundant classes inflate bundle size
- Visual regressions compound silently
Utility-driven Tailwind enforced:
- Deterministic styling
- Centralized design tokens
- Stable UI across mobile/web
CSS drift is operational risk.
Language Strategy
TypeScript
- Shared contracts across web, mobile, API
- Strict typing for tool inputs/outputs
- Safer refactoring at scale
Python
- Mature LLM SDK ecosystem
- Async orchestration
- Clean JSONL pipelines
- Transparent token accounting
Architecture is language-agnostic.
Governance is not.
Agent with Tools Model
The agent:
- Installs tools
- Uses tools (bounded by policy)
- Writes to filesystem
- Sends messages (e.g., WhatsApp integration)
- Logs every action
- Executes in constrained sequence
Policy.json governed:
- Context window size
- Token limits
- Response limits
Cost held to ~$0.02 per 100K tokens through bounded execution.
Autonomy without governance is chaos.
Autonomy with guardrails is scalable automation.
Architect-Level Signal
What this demonstrates:
- Implementation sequencing
- Environment reproducibility
- Policy-based LLM governance
- Observability-first design
- Test-before-commit enforcement
- Cross-platform stack orchestration
This is how you lead systems—not just build features.
From a Solution Architect lens:
Blueprint first.
Controlled tools.
Logged execution.
Inspectable checkpoints.
Reversible states.
That pattern scales—from repos to data centers.
How to use this article
Use this as a working lens for AI-assisted engineering workflows, intent capture, and tool-using delivery systems. If the problem is a software leadership evaluation, route it through TSmithCode proof. If the problem is a scoped automation, CAD platform, data, or delivery engagement, route it through CAD Guardian so the first phase has clear boundaries, acceptance evidence, and a handoff path.
Migrated image archive